At this year’s NICAR Data Journalism Summit, data journalists shared digital tools that are transforming investigative journalism.
This guide was originally published by GIJN on 16/3/2026 and is hereby reproduced by iMEdD with permission. Any reprint permissions are subject to the original publisher. Read the original guide here.
Main image: Yutong Liu & Kingston School of Art / https://betterimagesofai.org / https://creativecommons.org/licenses/by/4.0/
Access all tools here:
Dozens of leading data journalists shared some of their favorite digital tools and databases for investigating numerous topics at the recent NICAR data journalism summit.Easy, rapid geolocation is possible via a remarkable web-based data mining tool for OpenStreetMaps, called Overpass Turbo.
Previous NICAR events have showcased a diversity of head-turning tools, from the timeline YouTube transcriber Summarize.Tech to the journalist-friendly ship-tracking tool Vessel Viewer to Dangerzone, a free tool that scrubs malware from PDF leaks.
At NICAR 2026, several speakers noted new applications for familiar open source tools, such as OpenCorporates, Google Earth, and DocumentCloud.
But here, GIJN offers a curated list of new or rarely used tools that attracted deep interest among reporters at the event:
Overpass Turbo
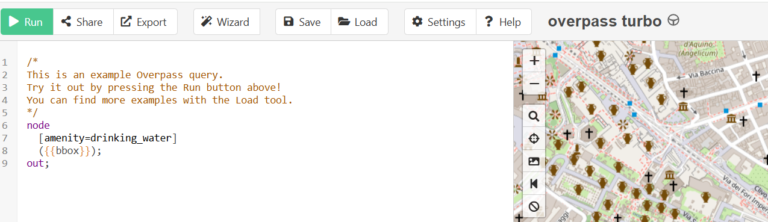
Imagine being able to locate a place in a photo just by typing in something like “show me places that have a fountain within 30 meters of a dog park in Lima, Peru,” or “show me all ‘1426’ street addresses in town-X, Turkey” — and then clicking “run” on a free website. AP reporter Larry Fenn told a NICAR audience that this kind of easy, rapid geolocation is possible via a remarkable web-based data mining tool for OpenStreetMaps, called Overpass Turbo.
“This is a very useful but also a very spooky tool,” said Fenn. “Spooky because you feel that any photo I take, it’s gonna geolocate me in the world.”
While searches on the tool are code-based, the game–changing tip Fenn also revealed is that reporters can simply ask an LLM chatbot to write that code, and then paste it back into the tool to find those places in minutes.
“The neat thing is you don’t need to learn Overpass Turbo language because you can just ask a tool like ChatGPT – which has now ingested the OpenStreetMap wiki, and so knows how the Overpass API works – and type [for instance] ‘Write an Overpass Turbo query to show me fast food restaurants in Puerto Vallarta, Mexico, within 25 meters of a hotel’,” he explained. “It’s extremely powerful.”
He added: “The key to making this technique work is to think of the map features OpenStreetMap is likely to have, because, as an open database, people contribute to it, so you have to think about landmarks people are going to be tagging. People love to tag features related to amenities – things like parks.”
However, while easy to query, the tool installation procedure is code-based, and the access protocols can be complex. A less comprehensive but simpler option is the Bellingcat OpenStreetMap Search tool, which includes simple sliders to define distances between a preset list of features to search for. In general, panelists recommended that reporters explore and experiment with Bellingcat’s excellent guide on numerous geolocation tools.
Deportation Data Project
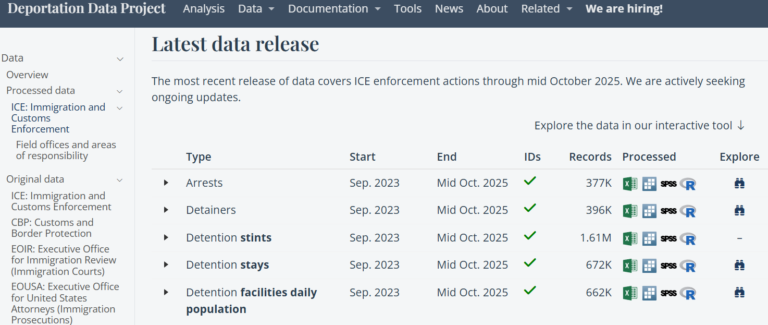
NICAR panelists noted that — thanks to tireless FOIA litigation by lawyers at UC Berkeley — the Deportation Data Project offers reporters stunningly detailed data on a topic of international focus in 2026: the millions of people caught in the various immigration enforcement nets in the United States. While the data is anonymized, it features individual-level arrest, detention, and deportation information from data acquired from Immigration and Customs Enforcement (ICE), Customs and Border Protection (CBP), and several other agencies. Remarkably, it even records details of each transfer between detention facilities, as well as incidents where asylum-seekers were turned away at ports of entry.
“This is one of the big datasets that we should all be using,” said Will Craft, data editor at the Guardian. “It is extremely detailed, down to the individual level. It allows you to track every single person arrested — through their arrest; through every single stay they have in every individual detention facility they’re booked into; through to their deportation.”
The portal does supply a data use explainer, as well as a “codebook” for understanding ICE data tables. However, Craft conceded that this vast dataset is still “ very hard to work with, and can’t really be opened in a spreadsheet.” As a result, panelists noted that Big Local News has partnered with the Deportation Data Project to produce an Immigration Enforcement Reporting Recipes tool to help reporters mine the resource with guides and simplified datasets. While he noted that it was currently running a week late on promised updates — and that each new data release deletes prior releases — Craft added that the DHS Detention Management Statistics database was also a good tool for basic data on immigration enforcement nationally.
Illicit Finance Data Lab
One hot-off-the-press resource that attracted attention at NICAR was this new project dedicated to building a cross-sector collaborative community to combat global corruption.
Co-founded by the Anti-Corruption Data Collective and the Organized Crime and Corruption Project (OCCRP), this site actively facilitates collaboration between researchers, data scientists, and investigative reporters — and is designed to quickly connect journalists with each other and with dirty money researchers. The site promises to offer practical and legal resources, story tip-offs, case studies, and high-level tip-sheets. To join, reporters need to apply via this link.
“I heard someone say: ‘We live in a great time to follow the money, because we now have all this data, it’s never been easier, and they’re doing it under our noses’ — but the problem is we don’t really have the team sizes or resources we need to get the most of this opportunity,” said Ezana Ćeman, product manager for OCCRP data platforms. “So in December, we launched Illicit Finance Data Lab in collaboration with the Anti-Corruption Data Collective, and we are gathering interest right now. We are actively bringing journalists, academics, and scientists together; different skills, so we can fight this transnational corruption as a united front.”
Bellingcat Telegram Phone Number Checker
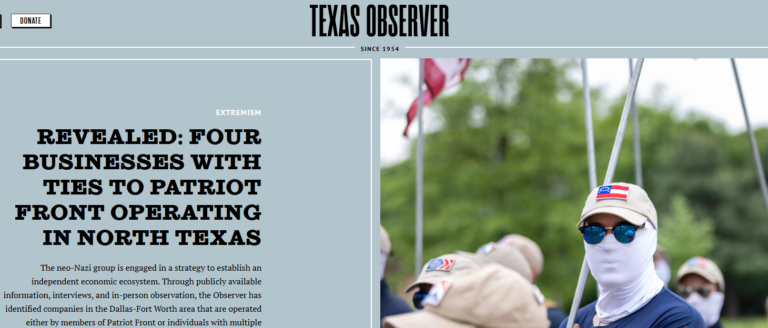
The Bellingcat Telegram Phone Checker tool helped Tristan Lee identify a network of businesses run by members of neo-Nazi groups this year. Image: Screenshot, Texas Observer
This is a free tool that requires “intermediate” computer science skills — specifically, command line abilities — and perhaps some IT help at the initial installation stage. But open source researchers say that, once it’s running, it offers a unique way to find more information on the owner of a phone number you already have, if that person owns a Telegram account. Or you can search multiple numbers in a batch, with numbers separated by commas. At the conference, Tristan Lee, co-founder of Decoherence Media, a nonprofit outlet that investigates extremist groups, described how he used this new tool to show that one business owner was also the owner of an extremist Telegram channel so hateful that it celebrated the holocaust even in its name.
“The phone number checker lets you know whether a phone number is registered on Telegram, and it tells you their username, if they haven’t set it to private,” he explained.
According to Bellingcat, the tool can extract these and other details — including names, profile photo, and when they were last online — by persuading the Telegram API to try to add the number as a contact on your own Telegram account. For this and other reasons, experts recommend that reporters not use their personal Telegram accounts for searches. Reporters can follow guidelines on use at this link, and the complex installation procedure via the Github page, or this video tutorial.
Specific Paid Databases Worth Accessing
Investigative reporters and under-resourced newsrooms almost always prefer free or open source tools, for both ethical and budget reasons. Many can be found within tools dashboards from leading investigative groups, such as the BBC Africa Eye Forensics Dashboard, or Craig Silverman’s Verification Handbook, or OCCRP’s country-by-country list of financial registries, and, of course, its Aleph Pro, with four billion records of leaks, sanctions, and corporate registries.
However, OCCRP’s Ezana Ćeman pointed out that some proprietary data services are so useful for specific projects that newsrooms may wish to consider alternate means of access — either through free trials, a borrowed login, short-term subscriptions, or direct requests for free access for an investigative project.
“Now, I know paid databases are not (so popular), but we wanted to include them because maybe someone connected to your newsroom has a login, or the local university might, and many of them offer free trials,” she said. “My experience is that if you just email many of these services — explaining the need, and saying ‘I’m not in a financial position to subscribe to your tool’ — they might help you.”
While not specifically endorsing any of these for a specific newsroom, Ćeman offered a list of paid-for databases that have helped OCCRP investigations, and that other newsrooms may wish to find some means of access. Below, GIJN shares a shorter version of this list, curated for less well-known tools, along with OCCRP’s notes.
- Factiva — “Archive of global news and industry insights; excellent for company mentions.”
- Spark Interfax — “Russian company registry with translations and transliterations, searchable by person or company; also shows offshore companies that have done business with Russia.”
- Sayari — “Global public records including court, trade, tax, and business registries; covers hard-to-access regions like China, Brazil, MENA, and Africa.”
- Offshore Alert — “Caribbean court document database; helpful for offshore entities involved with litigation.”
- Opensky Network — “Historical info for plane flights; a huge database collected from receivers all over the world, from signals from plane transponders.”
- Volza — “Provides global import-export data and trade insights.”
- Marine Traffic — “Vessel tracker, shows ship movements and port visits; our (OCCRP) account includes animated replays of vessel routes from the past five years and detailed behavior for the past year. Older data is costly.”
- Pipl.com — “Advanced people-search engine that links names, emails, usernames, and phone numbers; finds associated accounts and online traces.”
- Pimeyes — “Facial recognition tool that searches the web for similar faces to an uploaded photo; helps uncover media appearances, and does not search social media accounts.”
- Intelx.io — “Checks leaked records with phone numbers, emails, IP addresses.”
- IRBIS — “Powerful reverse-lookup tool; includes emails, phone numbers, and social media profiles.”
- Osint.industries — “Checks leaked records with numbers or emails, and usernames; all journalists can get a free account.”
- Darkside by District 4 Labs — “Checks leaked records with emails, phone numbers, and usernames.”
- Wirescreen — “Ownership information for China; flags if it is state-owned, if it is under sanctions, if its director is a Chinese Communist Party member, or if it’s part of the military supply chain.”
- Crystal Intelligence — “A blockchain intelligence tool for real-time screening of crypto transactions.”

